Copyright © 2005, 2006, 2007 Thomas M. Eastep
Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, with no Front-Cover, and with no Back-Cover Texts. A copy of the license is included in the section entitled “GNU Free Documentation License”.
2020/04/17
Table of Contents
One of the most misunderstood aspects of Shorewall is its relationship with routing. This article attempts to clear some of the fog that surrounds this issue.
As a general principle:
Routing determines where packets are to be sent.
Once routing determines where the packet is to go, the firewall (Shorewall) determines if the packet is allowed to go there.
There are ways that Shorewall can affect routing which are described in the following sections.
The following diagram shows the relationship between routing decisions and Netfilter.
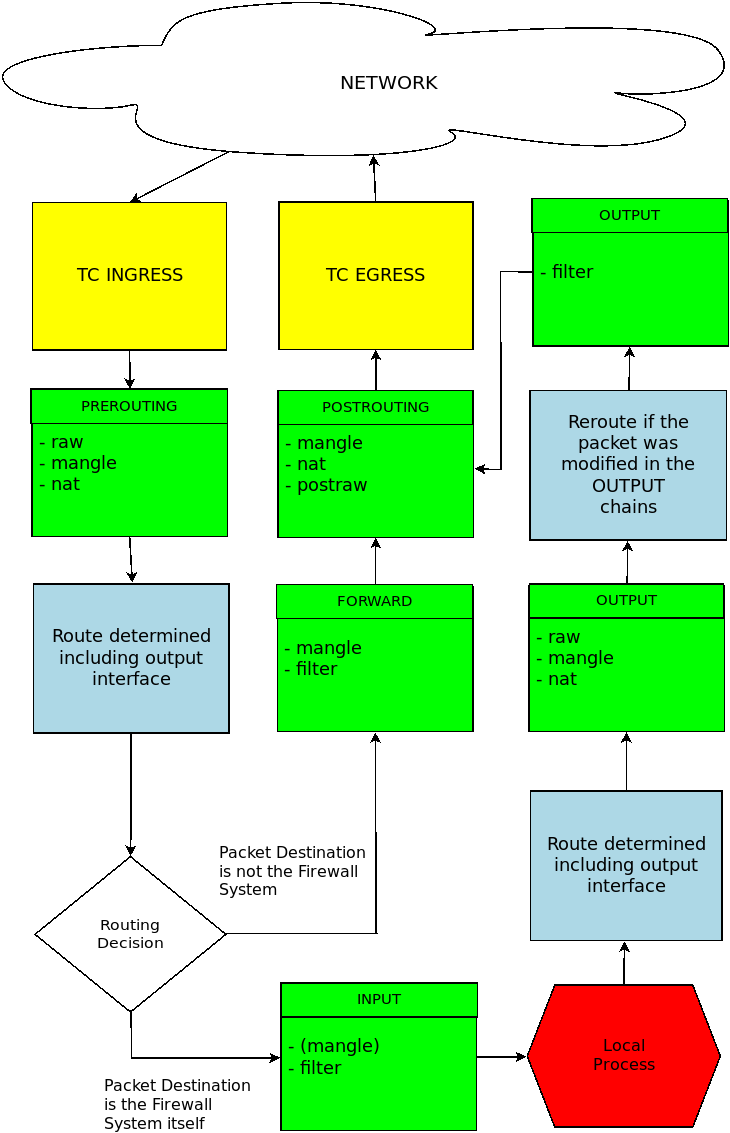
The light blue boxes indicate where routing decisions are made. Upon exit from one of these boxes, if the packet is being sent to another system then the interface and the next hop have been uniquely determined.
The green boxes show where Netfilter processing takes place (as directed by Shorewall). You will notice that there are two different paths through this maze, depending on where the packet originates. We will look at each of these separately.
When a packet arrives from outside, it first undergoes Netfilter PREROUTING processing. In Shorewall terms:
Packets may be marked using entries in the /etc/shorewall/mangle (/etc/shorewall/tcrules) file. Entries in that file containing ":P" in the mark column are applied here as are rules that default to the MARK_IN_FORWARD_CHAIN=No setting in
/etc/shorewall/shorewall.conf. These marks may be used to specify that the packet should be routed using an alternate routing table; see the Shorewall Squid documentation for examples.Caution
Marking packets then using the fwmark selector in your "ip rule add" commands should NOT be your first choice. In most cases, you can use the from or dev selector instead.
The destination IP address may be rewritten as a consequence of:
DNAT[-] rules.
REDIRECT[-] rules.
Entries in
/etc/shorewall/nat.
So the only influence that Shorewall has over where these packets go is via NAT or by marking them so that they may be routed using an alternate routing table.
Processing of packets that originate on the firewall itself are initially routed using the default routing table then passed through the OUTPUT chains. Shorewall can influence what happens here:
Packets may be marked using entries in the /etc/shorewall/mangle (/etc/shorewall/tcrules) file (rules with "$FW" in the SOURCE column). These marks may be used to specify that the packet should be re-routed using an alternate routing table.
The destination IP address may be rewritten as a consequence of:
DNAT[-] rules that specify $FW as the SOURCE.
Entries in
/etc/shorewall/natthat have "Yes" in LOCAL column.
So again in this case, the only influence that Shorewall has over the packet destination is NAT or marking.
The Shorewall 2.x Shorewall
Squid documentation shows how alternate routing tables can be
created and used. That documentation shows how you can use logic in
/etc/shorewall/init to create and populate an
alternate table and to add a routing rule for its use. It is fine to use
that technique so long as you understand that you are basically just using
the Shorewall init script (/etc/init.d/shorewall) to
configure your alternate routing table at boot time and that other than as described in the previous section, there is no
connection between Shorewall and routing when using Shorewall versions
prior to 2.3.2.
There is one instance where Shorewall creates main routing table
entries. When an entry in /etc/shorewall/proxyarp
contains "No" in the HAVEROUTE column then Shorewall will create a host
route to the IP address listed in the ADDRESS column through the interface
named in the INTERFACE column. This is the only case
where Shorewall directly manipulates the main routing
table.
Example:
/etc/shorewall/proxyarp:
#ADDRESS INTERFACE EXTERNAL HAVEROUTE PERSISTENT 206.124.146.177 eth1 eth0 No
The above entry will cause Shorewall to execute the following command:
ip route add 206.124.146.177 dev eth1Beginning with Shorewall 2.3.2, support is included for multiple Internet connections. If you wish to use this feature, we recommend strongly that you upgrade to version 2.4.2 or later.
Shorewall multi-ISP support is now covered in a separate article.

